-
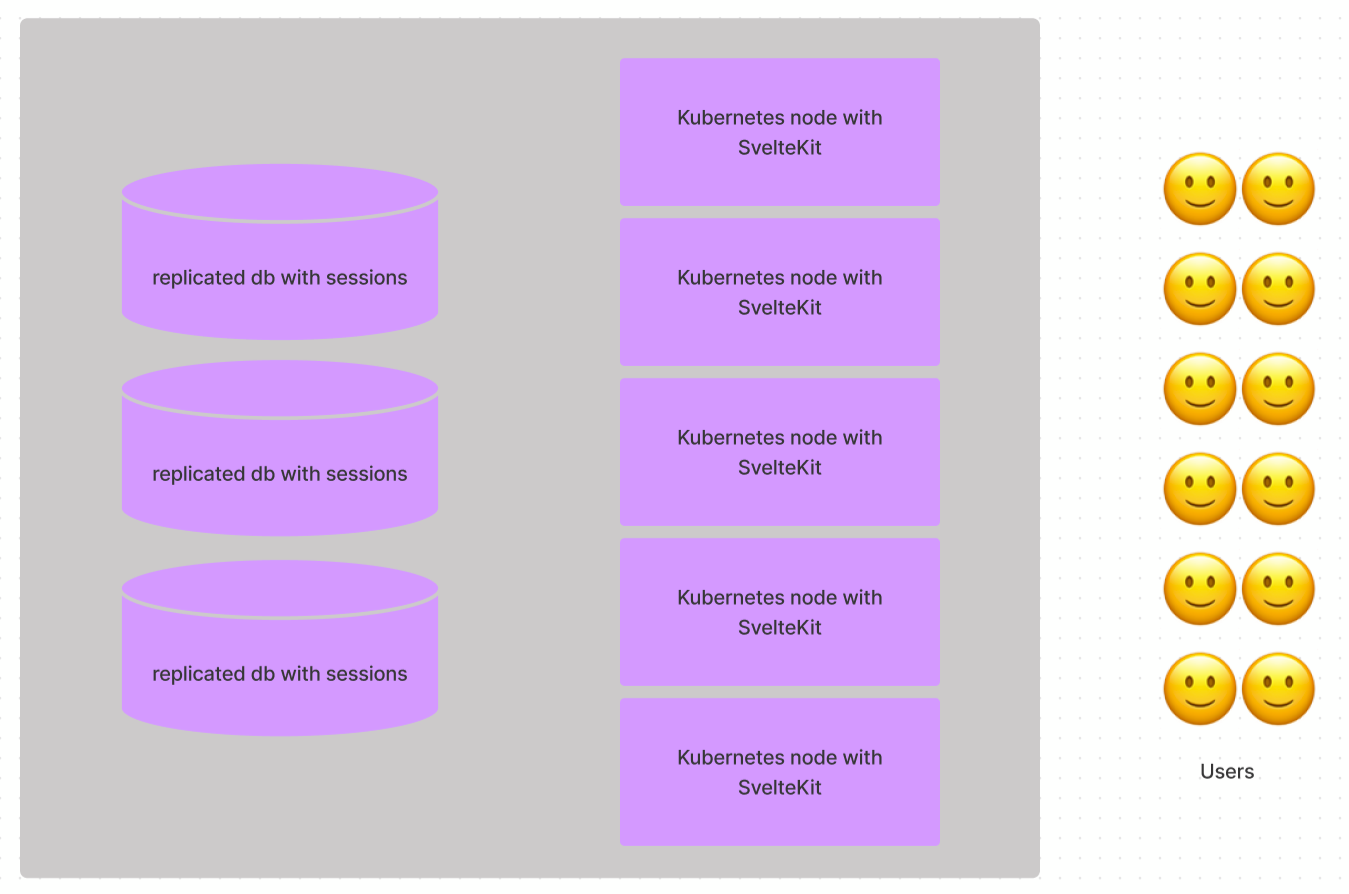
Describe the problemFrom the docs, in particular the part about With express I would store session data on a database, single instance or replicated and get always the session from there. Hence, I can scale express indefinitely since it stays stateless. Is this also possible with SvelteKit? Meaning Svelte's session store would always get the session data from a db before it answers the request? A simple chart of such an architecture: The problem behind: Even if some cluster orchestration software allows to create sticky sessions, so requests hit the same node, it is not always possible to solve this problem on the cluster layer (e.g., when using BGP, autoscaling down, etc.) and it's in general more complicated than just storing the sessions on the db if latter is fast. Describe the proposed solutionA paragraph in the docs stating if deploying to a multi-node cluster is possible and/or what trade-offs would be encountered (assuming the cluster layer does not offer sticky sessions). Alternatives consideredNo response Importancewould make my life easier Additional InformationNo response |
Beta Was this translation helpful? Give feedback.
Replies: 4 comments 7 replies
-
|
Session handling is left up to you, using the provided hooks. In the configuration you're describing, you would write a Which means that scaling up would not be a problem, because session data would always be fetched from the DB service no matter which node answered the request. |
Beta Was this translation helpful? Give feedback.
-
|
Ok, glad to hear and to summarize:
Did I get it right? |
Beta Was this translation helpful? Give feedback.
-
|
You can improve your scalability further by making the session cookie data into a bearer token (JWT) This means you only need to do the database lookup when you are signing in or refreshing the access token, rather than on every single HTTP request. The request effectively contains all the data needed to create the response (from a user info / permission perspective). The token is typically signed so you can verify that it hasn't been tampered with but this is a quick operation without any network request or database lookup (you should really do this even if using the DB sessions, so it's not extra work). |
Beta Was this translation helpful? Give feedback.
-
But how would I invalidate existing JWT tokens out in the wild if "it is just a quick operation without any network request or database lookup"? |
Beta Was this translation helpful? Give feedback.
Session handling is left up to you, using the provided hooks. In the configuration you're describing, you would write a
handlehook runs first, takes the request, and extracts (for example) a session ID from a cookie and attaches that session ID torequest.locals. Then thegetSessionhook would run, talk to the database and fetch the session data given the session ID, and return an object with the session data that the client should see (which will populate the$sessionstore on the client). (Note: You could also do the DB query in thehandlehook rather than thegetSessionhook, depending on whether you want that session data loaded for endpoints or just for pages. The best way to do tha…