#What droidefense is
droidefense (originally named atom: analysis through observation machine)* is the codename for android apps/malware analysis/reversing tool. It was built focused on security issues and tricks that malware researcher have on they every day work. For those situations on where the malware has anti-analysis routines, droidefense attemps to bypass them in order to get to the code and 'bad boy' routine. Sometimes those techniques can be virtual machine detection, emulator detection, self certificate checking, pipes detection. tracer pid check, and so on.
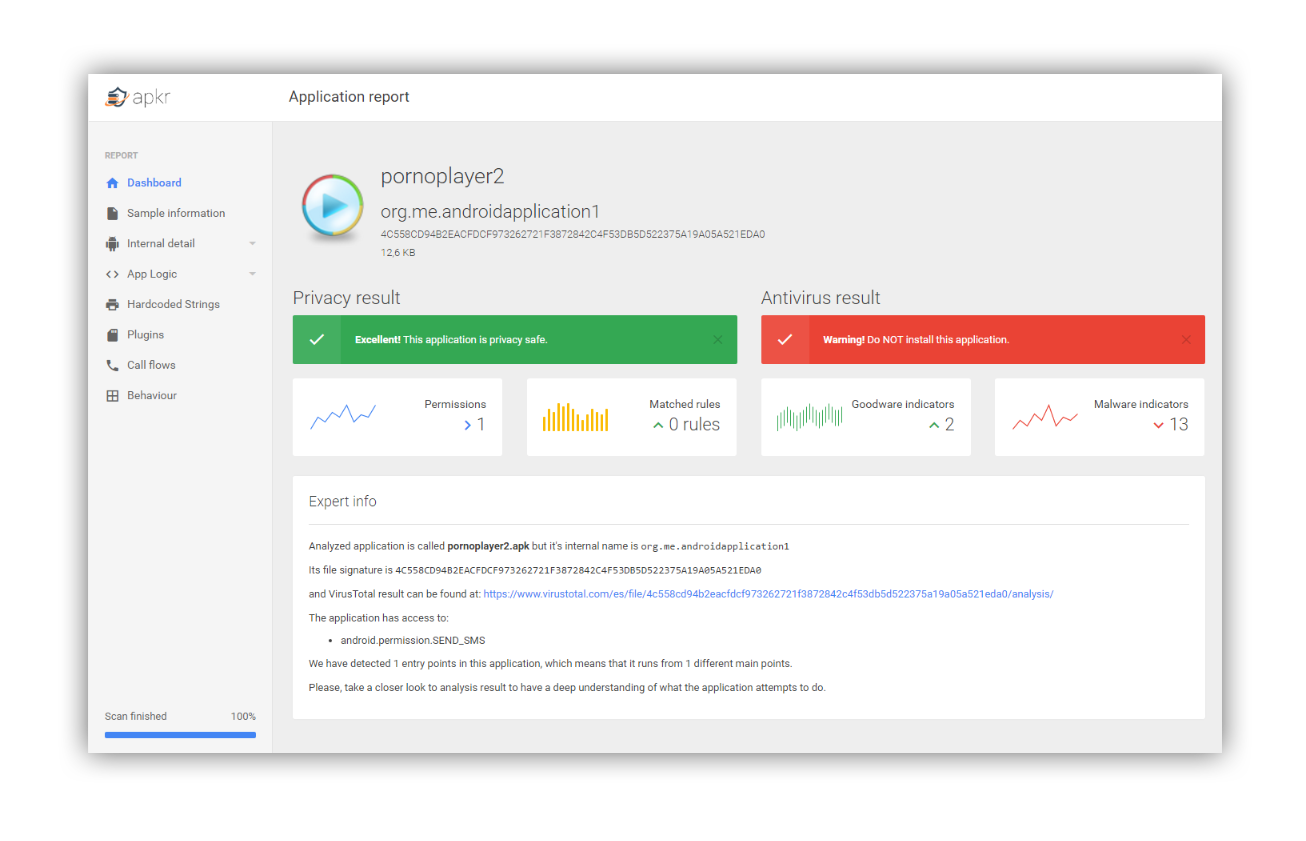
droidefense uses an innovative idea in where the code is not decompiled rather than viewed. This allow us to get the global view of the execution workflow of the code with a 100% accuracy on gathered information. With this situation, droidefense generates a fancy html report with the results for an easy understanding.
To support this project you can:
- Post thoughts about new features/optimizations that important to you
- Submit bug using one of following ways:
- Error stacktrace string and log files.
- Error log and link to public available apk file.
- Do NOT forget to fullfil issue template
And any other comments will be very appreciate.
#License
This program is free software: you can redistribute it and/or modify it under the terms of the GNU General Public License as published by the Free Software Foundation, either version 3 of the License, or (at your option) any later version.