New issue
Have a question about this project? Sign up for a free GitHub account to open an issue and contact its maintainers and the community.
By clicking “Sign up for GitHub”, you agree to our terms of service and privacy statement. We’ll occasionally send you account related emails.
Already on GitHub? Sign in to your account
Problem with IP Restriction rules in azurerm_app_service resource #2488
Comments
|
Up until last week this was a nuisance but today when I logged in to check a azure web app in the portal the iprestrictions blade is broken because of this. The gui fails because of a null reference when trying to apply "tolower" to a property which makes me suspect the name property of the rule. If I use https://resources.azure.com/ to find the ip restriction rule in the app and add a name property to the rule the iprestrictions blade loads normally. |
|
We are experiencing the same issues. |
|
This bug do our use of Terraform terrible. Without possible to add priority and name, our app service, would not work. This bug cause us to must add a manual step, where we must remember config this in portal after apply. |
|
In cases like this we usually use Powershell script. |
|
Has this issue been fixed yet? |
|
@turjachaudhuri, unfortunately no, it has to be fixed in next release (1.23) but it was moved to 1.25 release... |
|
Has this issue been fixed ? in Azure provider 1.25 version ? Or in any later version ? Can somebody let me know. |
|
No it hasn't which is annoying as it would be really useful to label the IP addresses in the portal. |
|
While we wait for this to be updated the following code using azurerm templates can set the resource "azurerm_template_deployment" "ipwhitelist" {
name = "${var.application}-ipwhitelist"
resource_group_name = var.resource_group_name
template_body = <<JSON
{
"$schema": "https://schema.management.azure.com/schemas/2015-01-01/deploymentTemplate.json#",
"contentVersion": "1.0.0.0",
"variables": {
"_force_terraform_to_always_redeploy": "${timestamp()}"
},
"resources": [{
"type":"Microsoft.Web/sites/config",
"apiVersion":"2018-11-01",
"name":"${azurerm_app_service.app_service.name}/web",
"location":"[resourceGroup().location]",
"properties":{
"IpSecurityRestrictions":[
{
"ipAddress":"${local.some_address_to_allow}",
"action":"Allow",
"tag":"Default",
"priority":300,
"name":"Allow_My_Proxy",
"description":"useful info"
}
],
"scmIpSecurityRestrictions":[
{
"ipAddress":"${local.some_address_to_allow}",
"action":"Allow",
"tag":"Default",
"priority":300,
"name":"Allow_My_Proxy",
"description":"useful info"
}
]
}
}
]
}
JSON
deployment_mode = "Incremental"
} |
|
Is there a way to use ip_restriction with Type as 'Virtual Network' using Terraform? |
|
To add it as VNet restriction you use But was there any progress on adding names and priorities? |
|
@JleruOHeP yes, there is just now an open PR for names and priorities :) #6705 |
|
I am facing the same issue, was this fixed ? |
|
I'm pretty sure that this now works, other than some issues with changing between ip and subnet. or Note setting both |
|
Hi @martinjt , Seems those rules are not supported yet. I'm right? |
|
I've not seen that in the terraform docs. |
|
have just upgraded to v2.43 and tried to get this working with the documentation on https://registry.terraform.io/providers/hashicorp/azurerm/latest/docs/resources/function_app but ran into the following issues with the below configuration: This resulted in the following error when executing plan: If I then add the apparently (although the documentation says otherwise) required fields with empty values like below: I run into the following errors when executing plan: |
|
for completeness sake, the documentation currently says the following: |
|
I am running into the same issue as @mrboogiee When adding these params as per error message with some dummy values i get the following error: I got it working with |
|
Any chances it might be fixed anytime soon? |
|
I don't like leaving maybe-this-is-related comments in an issue, but... well, this could be related to the original issue. This issue was opened when azurerm_app_service was the resource; we are using the new azurerm_linux_web_app but apparently it works the same way. I can't get Terraform to clear the ip_restriction list. I can change the entries by specifying different values. But I can't remove all entries. If I specify an empty list ( Apparently ip_restriction uses Attributes-as-Blocks syntax underneath, so simply removing the blocks from the configuration -- or using dynamic blocks, which does the same thing -- causes Terraform to ignore any existing entries rather than remove them. For that kind of block you have to specify an empty list. But I tried just removing the blocks anyway, and it does indeed ignore the existing entry; the plan shows no action. Per the linked Terraform doc, attributes as blocks is a legacy implementation and this might explain why things don't work, but of course now I'm just speculating. |
|
Hi guys, have anybody used this approach? |
|
Hey all i am going to close this because the If this is still an issue with |
Hi,
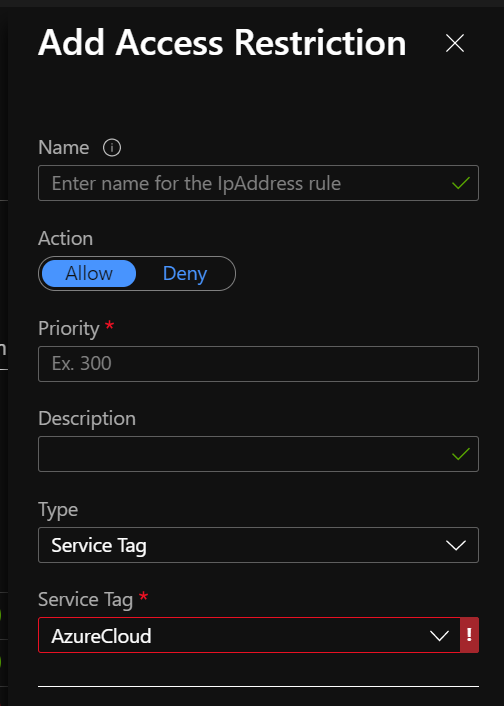
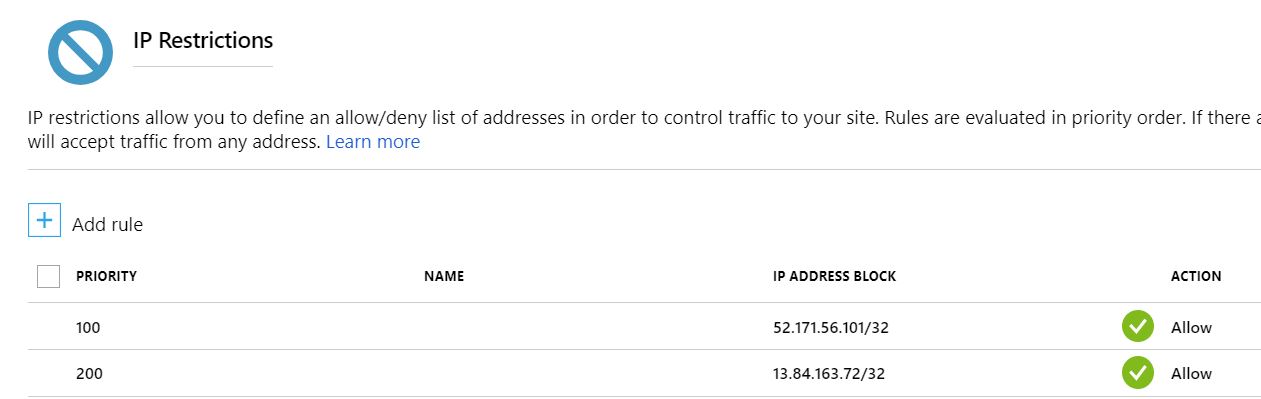
We stepped into the strange problem while working with "IP Restriction" azurerm_app_service resource functionality. There is a need to manage this IP Restriction rules externally by using PowerShell script and not with Terraform. Below are detailed steps we followed:
We successfully applied needed restriction rules via script.
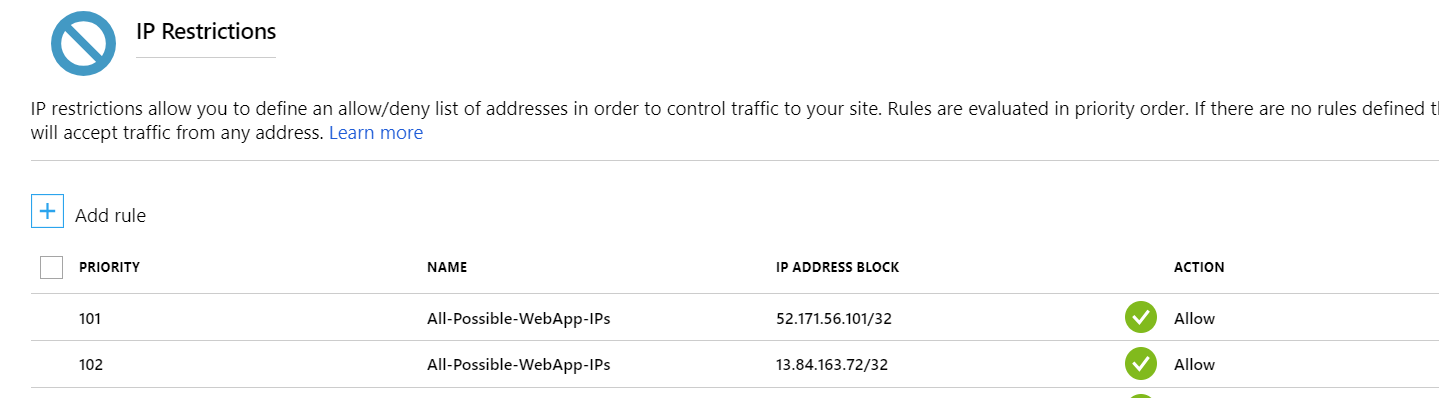
Then we decided to change tags (basically any change) for app_service resource via TF. After that rules became broken and we see this:
I've tried to add IP Restriction list to Lifecycle->Ignore Changes part of the app_service resource, like this:
lifecycle {
ignore_changes = [
"site_config.0.scm_type",
"site_config.0.ip_restriction"
]
}
But this does not help whenever we change IP restriction rules externally and then apply TF, rules became broken.
At the same time, looks like, current implementation of azurerm_app_service resource IP Restriction part is using old Azure API 2016-08-01 instead of 2018-02-01 (https://docs.microsoft.com/en-us/azure/app-service/app-service-ip-restrictions). In old API you need just to specify 2 parameters: ip_address and subnet_mask. But for new API ip_restriction consists of the next parameters:
{
"ipAddress": "131.107.159.0/24",
"action": "Allow",
"tag": "Default",
"priority": 100,
"name": "allowed access"
}
So basically when TF Apply run against app_service resource it is using old API and this just break IP Restriction rules at all.
So I have two questions:
Community Note
Terraform (and AzureRM Provider) Version
Terraform v0.11.7
Affected Resource(s)
Terraform Configuration Files
Debug Output
Panic Output
Expected Behavior
Actual Behavior
Steps to Reproduce
terraform applyImportant Factoids
References
The text was updated successfully, but these errors were encountered: